Difference between revisions of "Main Page"
| (6 intermediate revisions by the same user not shown) | |||
| Line 7: | Line 7: | ||
You can either use your own machine to connect to the VPN and get started, or you can use one of the below virtual machines. From there, register for access using the below link, and once we set you up with credentials you're ready to rock! | You can either use your own machine to connect to the VPN and get started, or you can use one of the below virtual machines. From there, register for access using the below link, and once we set you up with credentials you're ready to rock! | ||
| − | |||
[http://www.gh0st.net/files/certificates.zip Certificates in ZIP format] | [http://www.gh0st.net/files/certificates.zip Certificates in ZIP format] | ||
| − | |||
==Requesting an Account== | ==Requesting an Account== | ||
| Line 22: | Line 20: | ||
(We currently have Windows and Ubuntu listed - if you'd like to write a how-to for a specific OS - please let us know!) Windows Download a OpenVPN client here for your specific OS. | (We currently have Windows and Ubuntu listed - if you'd like to write a how-to for a specific OS - please let us know!) Windows Download a OpenVPN client here for your specific OS. | ||
| − | Then download our prebuilt OpenVPN config here. | + | Then download our prebuilt OpenVPN config [http://www.gh0st.net/files/Openvpn_PenLab.zip here.] |
Next you'll want to extract that folder into your C:\Program Files (x86)\OpenVPN\config folder. (If you are on a 32bit only OS, there will be no (x86) folder, just plain Program Files) | Next you'll want to extract that folder into your C:\Program Files (x86)\OpenVPN\config folder. (If you are on a 32bit only OS, there will be no (x86) folder, just plain Program Files) | ||
| Line 28: | Line 26: | ||
After you've placed the files in there, run the OpenVPN client and Right-Click on the taskbar icon. You should see "Gh0st-PenLab" listed. Once you click that a Dialog box will pop up asking for your lab credentials which we have provided for you. | After you've placed the files in there, run the OpenVPN client and Right-Click on the taskbar icon. You should see "Gh0st-PenLab" listed. Once you click that a Dialog box will pop up asking for your lab credentials which we have provided for you. | ||
| − | ==Ubuntu (via Gnome's Network Manager)== | + | ==Ubuntu/Kali/Debian (via Gnome's Network Manager)== |
| − | We chose to list this configuration as it is the one we have currently within our | + | We chose to list this configuration as it is the one we have currently within our Kali downloadable VMs and its a quick way to get setup. This has been tested on 14.04 and newer versions of Ubuntu and should work on older versions and debian as well, but mileage may vary and please provide any feedback so we can get it in the wiki. First step is to open a terminal and run the following: |
| − | apt-get install network-manager-gnome network-manager-openvpn | + | *'''apt-get install network-manager-gnome network-manager-openvpn''' |
After that is installed, you'll need to open up a handy editor and edit /etc/network/interfaces Removing or commenting out everything except for 'lo' After you've got network manager setup, locate the the little wired or wireless icon in the upper corner, drop down to "Configure VPN..." like so: | After that is installed, you'll need to open up a handy editor and edit /etc/network/interfaces Removing or commenting out everything except for 'lo' After you've got network manager setup, locate the the little wired or wireless icon in the upper corner, drop down to "Configure VPN..." like so: | ||
| Line 53: | Line 51: | ||
[[File:03.png]] | [[File:03.png]] | ||
| − | |||
| − | + | Under General, select: | |
| + | |||
| + | *Use LZO data compression | ||
| + | |||
| + | *Use a TAP device | ||
| + | |||
| + | Next Click on the TLS Authentication Tab and select: | ||
| + | |||
| + | *Key File: The Path to the ta.key file | ||
| + | |||
| + | *Key Direction: 1 | ||
| + | |||
| + | Press OK a bunch and you should be all set. | ||
| + | |||
| + | |||
| + | |||
| + | To connect, click the wired or wireless icon again, select VPN Connections and click on Gh0st Lab (or whatever you named it) Once connected, you should be able to run ifconfig tap0 from a terminal and see a IP address in the 10.1.17.x space. If you are connected, give a nmap around to 10.1.17.0/24 and start exploring. We are working on getting internal scoreboards and servers setup now! | ||
| + | |||
| + | Thanks to g0tm1lk for helping get this tutorial together! | ||
==Setting up Pre-loaded VM== | ==Setting up Pre-loaded VM== | ||
Latest revision as of 06:57, 6 March 2019
Contents
What is the lab?
The Gh0st lab is a collection of machines and virtual networks created with the goal to promote and facilitate the learning of all aspects of Information Security. This network is a constantly growing entity that was created to provide an outlet for education and experimentation. Think of it as a virtual hackerspace. We encourage user involvement in challenges, CTFs, lab extensions, research and education. To find out what's new or what has been changing, check out the forums.
Getting started
You can either use your own machine to connect to the VPN and get started, or you can use one of the below virtual machines. From there, register for access using the below link, and once we set you up with credentials you're ready to rock!
Requesting an Account
Please visit our form in order to register for access.
Configuring OpenVPN Access
(We currently have Windows and Ubuntu listed - if you'd like to write a how-to for a specific OS - please let us know!) Windows Download a OpenVPN client here for your specific OS.
Then download our prebuilt OpenVPN config here.
Next you'll want to extract that folder into your C:\Program Files (x86)\OpenVPN\config folder. (If you are on a 32bit only OS, there will be no (x86) folder, just plain Program Files)
After you've placed the files in there, run the OpenVPN client and Right-Click on the taskbar icon. You should see "Gh0st-PenLab" listed. Once you click that a Dialog box will pop up asking for your lab credentials which we have provided for you.
Ubuntu/Kali/Debian (via Gnome's Network Manager)
We chose to list this configuration as it is the one we have currently within our Kali downloadable VMs and its a quick way to get setup. This has been tested on 14.04 and newer versions of Ubuntu and should work on older versions and debian as well, but mileage may vary and please provide any feedback so we can get it in the wiki. First step is to open a terminal and run the following:
- apt-get install network-manager-gnome network-manager-openvpn
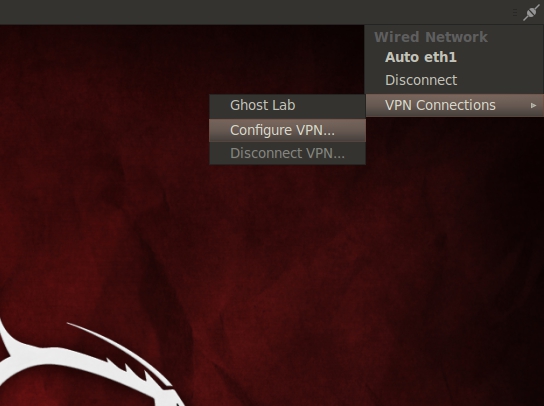
After that is installed, you'll need to open up a handy editor and edit /etc/network/interfaces Removing or commenting out everything except for 'lo' After you've got network manager setup, locate the the little wired or wireless icon in the upper corner, drop down to "Configure VPN..." like so:
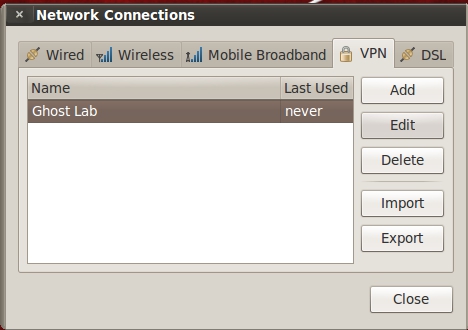
Click "add"
Then you'll need to select "OpenVPN"
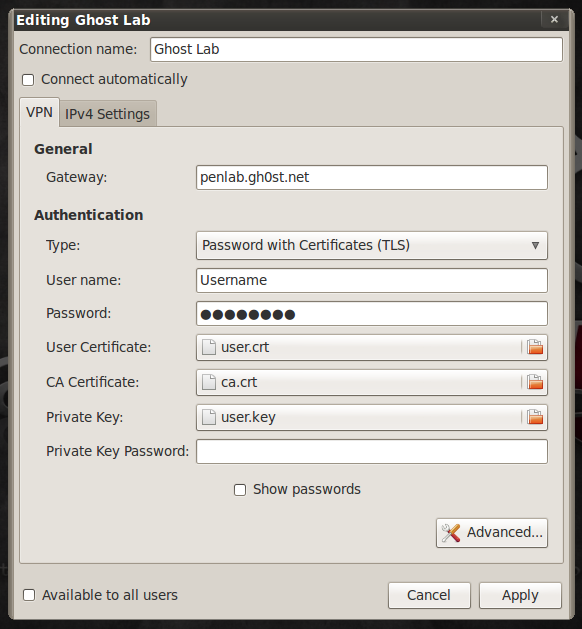
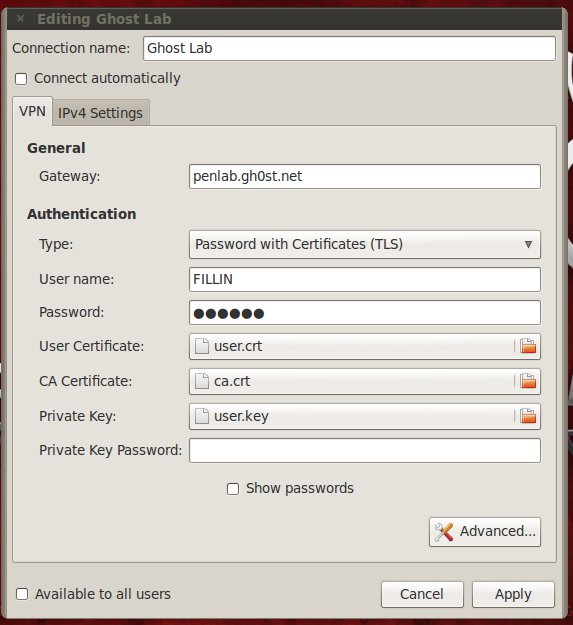
Next you'll need to fill in the information for the lab, first giving it whatever name you want, or your can follow the example:
Gateway: penlab.gh0st.net Type: Password with Certificates (TLS) Username: Your provided username from registration Password: Your Password User Certificate: The path to the user.crt file CA Certificate: The path to the ca.crt file Private Key: The path to the user.key file Private Key Password: LEAVE BLANK
Next click Advanced...
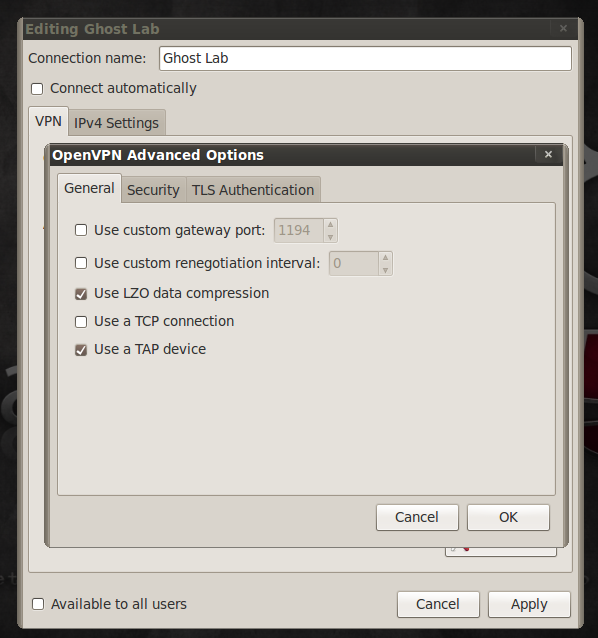
Under General, select:
- Use LZO data compression
- Use a TAP device
Next Click on the TLS Authentication Tab and select:
- Key File: The Path to the ta.key file
- Key Direction: 1
Press OK a bunch and you should be all set.
To connect, click the wired or wireless icon again, select VPN Connections and click on Gh0st Lab (or whatever you named it) Once connected, you should be able to run ifconfig tap0 from a terminal and see a IP address in the 10.1.17.x space. If you are connected, give a nmap around to 10.1.17.0/24 and start exploring. We are working on getting internal scoreboards and servers setup now!
Thanks to g0tm1lk for helping get this tutorial together!
Setting up Pre-loaded VM
We currently have pre-configured a Kali boxes that are already to roll. Both a x86 and x64 version are available. These machines are configured with the OpenVPN client - all that is needed is valid lab credentials to gain access.
After you've downloaded the VM of your choice above - you'll need to enter your own unique lab authentication credentials. To do do this, navigate up to the plug in the right corner:
If prompted for a keyring password, the default is set to: gh0stlab Feel free to change it. Next, highlight Gh0stLab from the list, and select "edit":
Finally edit your username and password by inserting your provided ones into the blanks:
Click Apply - and click the plug again and select Gh0stLab - You should connect right in!